
US Government🇺🇸
Quantum Security
Dashboard
A comprehensive audit of federal data breach vulnerabilities, quantum threat exposure, and Post-Quantum Cryptography migration readiness across 12 key federal departments and agencies.

The Impending Quantum Threat
The NSA has published CNSA 2.0 algorithm requirements and urged all National Security Systems to begin migrating to quantum-resistant cryptography immediately. The White House NSM-10 and OMB M-23-02 mandate federal agencies to inventory and transition their cryptographic systems.
Harvest Now, Decrypt Later
Nation-state adversaries are actively intercepting and storing encrypted US federal data today, planning to decrypt it once cryptographically relevant quantum computers become operational. NSA has flagged this as a priority concern.
Real-Time System Compromise
Once operational, quantum computers will break the RSA and ECC encryption protecting federal communications, digital signatures, VPNs, and secure access across all government systems and National Security Systems (NSS).
Legacy System Exposure
GAO's 2025 High Risk List identifies federal cybersecurity as a top concern. Over 300 legacy IT systems across agencies have unknown quantum vulnerability, with many lacking funded remediation plans.
Quantum Threat Timeline vs. Federal PQC Readiness (2020–2035)
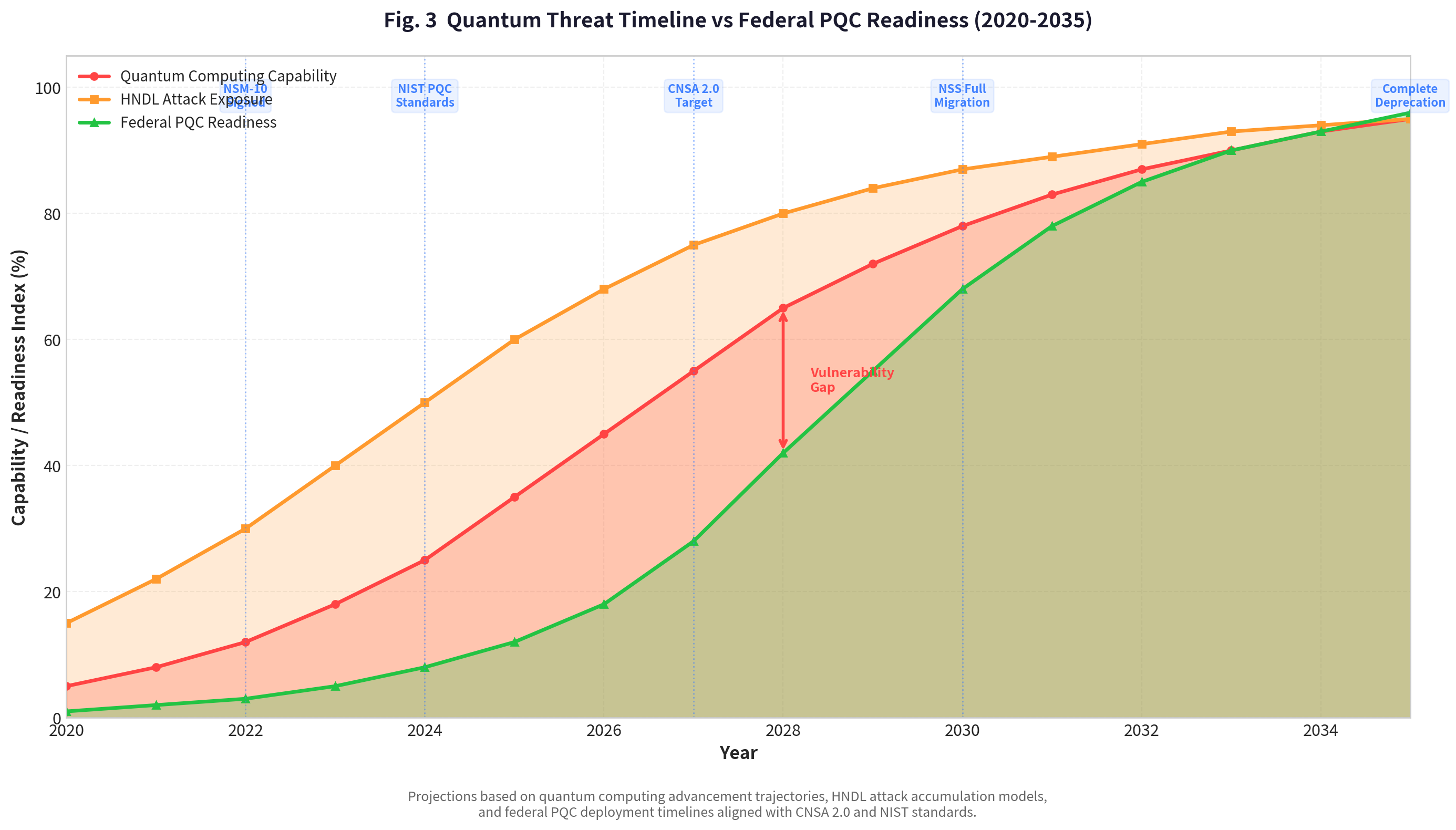
This chart illustrates the growing gap between escalating quantum computing capability and current federal PQC readiness. Key milestones include NSM-10 (2022), NIST PQC Standards (2024), CNSA 2.0 target (2027), and full NSS migration (2030). The 'Vulnerability Gap' represents the period during which critical federal data and systems remain exposed.
US Federal Data Breaches
Analysis of OMB FISMA reports, CISA incident data, and GAO cybersecurity assessments reveals a persistent and escalating challenge. Over 32,000 cybersecurity incidents were reported by federal agencies in FY2023 alone — a 10% increase year-over-year. Key agencies such as DOD, HHS, OPM, and Treasury remain high-value targets for state-sponsored adversaries.
Key Finding
The 2015 OPM breach exposed 22 million records including security clearance data. The 2024 Treasury breach via BeyondTrust involved Chinese state actors. The SolarWinds supply-chain attack compromised 18,000+ organizations including multiple federal agencies. These incidents demonstrate that adversaries are already targeting the exact systems that quantum computing will render completely indefensible — every breach today represents data that can be decrypted in the quantum future.
Federal Agency Data Breach Impact Analysis (FY2020–2025)

Bubble chart visualizing breach impact across 12 federal departments. Position indicates incident count and severity; bubble size represents volume of records exposed (millions). Data from OMB FISMA reports and CISA incident tracking.
Breach Type Distribution by Federal Department
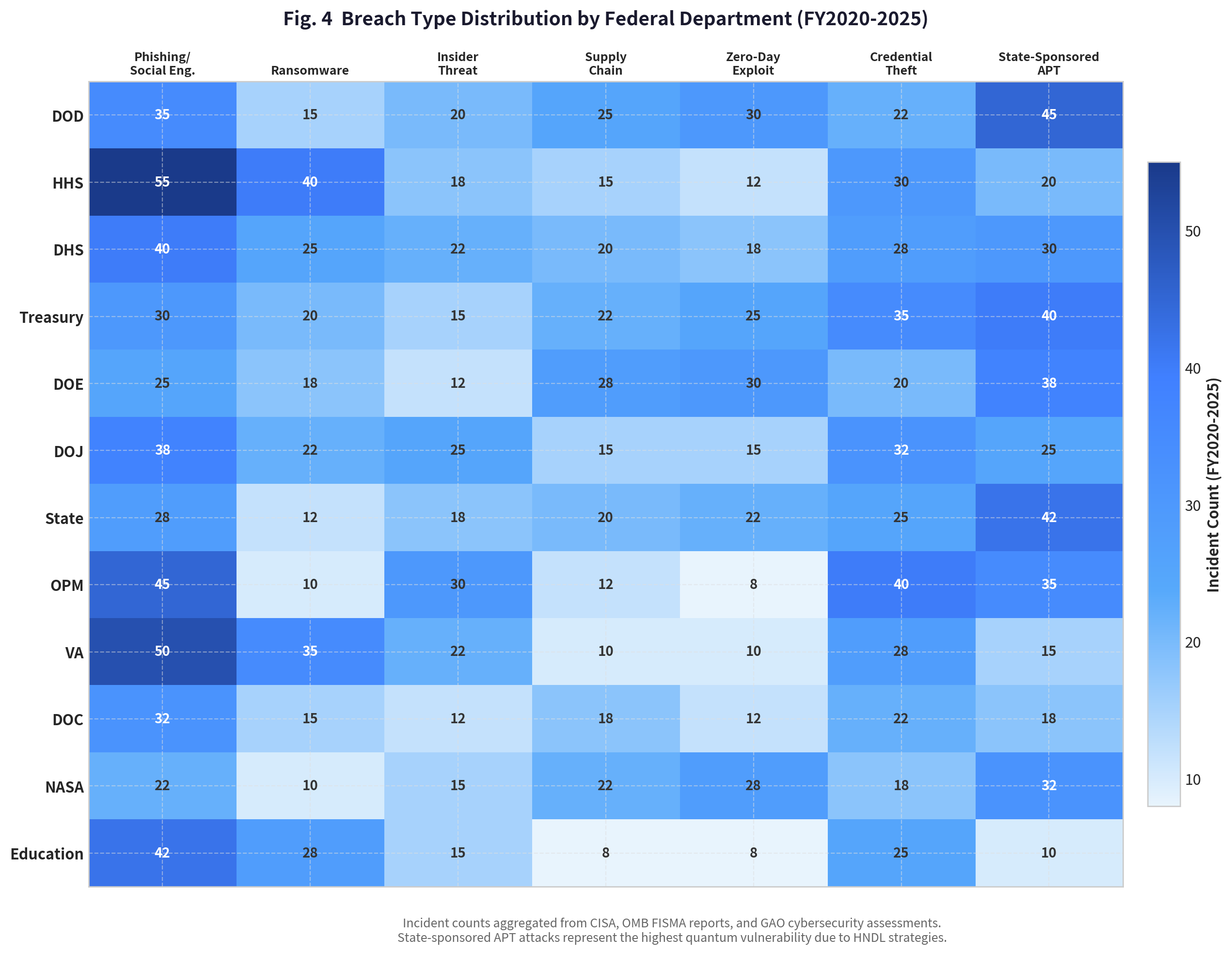
Heatmap showing the distribution of breach types across federal departments, highlighting the prevalence of state-sponsored APT attacks, phishing, credential theft, and supply chain compromises — all vectors amplified by quantum computing.
Departmental Risk Assessment
Qualitative risk assessment across 12 key federal departments and agencies, evaluated against six critical quantum risk dimensions including data sensitivity, legacy exposure, HNDL risk, and alignment with CNSA 2.0 requirements.
Department Quantum Risk Overview
| Department | Risk Score | Breaches | Cost Exposure | PQC Readiness |
|---|---|---|---|---|
01 DOD | 9.5 | 45 | $4500M | 15% |
02 HHS | 8.8 | 68 | $1800M | 10% |
03 DHS | 8.2 | 52 | $1200M | 20% |
04 Treasury | 9.0 | 38 | $1500M | 14% |
05 DOE | 8.7 | 35 | $1100M | 15% |
06 DOJ | 7.8 | 42 | $700M | 15% |
07 State | 8.3 | 30 | $650M | 18% |
08 OPM | 8.5 | 15 | $500M | 10% |
09 VA | 7.5 | 55 | $900M | 12% |
10 DOC | 6.2 | 22 | $250M | 15% |
11 NASA | 7.8 | 18 | $600M | 22% |
12 Education | 5.8 | 28 | $200M | 10% |
Quantum Vulnerability Risk Assessment by Federal Department
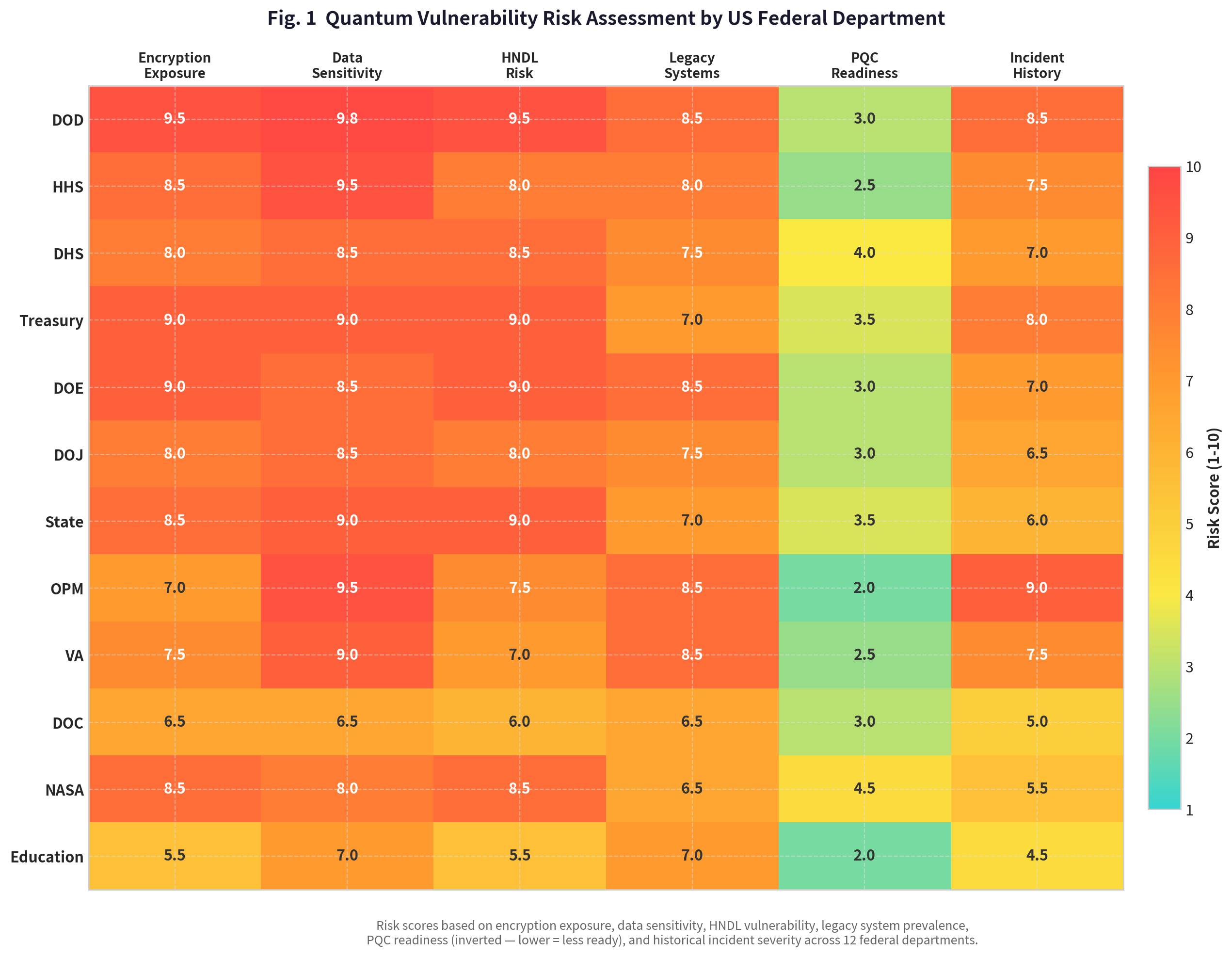
Comprehensive risk assessment of US federal departments against key quantum vulnerability indicators. Scores are on a 1-10 scale, with higher scores indicating greater risk. PQC Readiness is inverted (lower = less ready). Data sourced from GAO, CISA, and OMB FISMA reports.
The Staggering Cost of Inaction
The average cost of a US data breach hit an all-time high of $10.22 million in 2025 (IBM). Projections based on current cybercrime growth trajectories and the escalating quantum threat indicate a potential cumulative cost to the US federal government of over $304 billion by 2035 if PQC migration is not completed.
Projected Cost of Federal Quantum Insecurity (2025–2035)
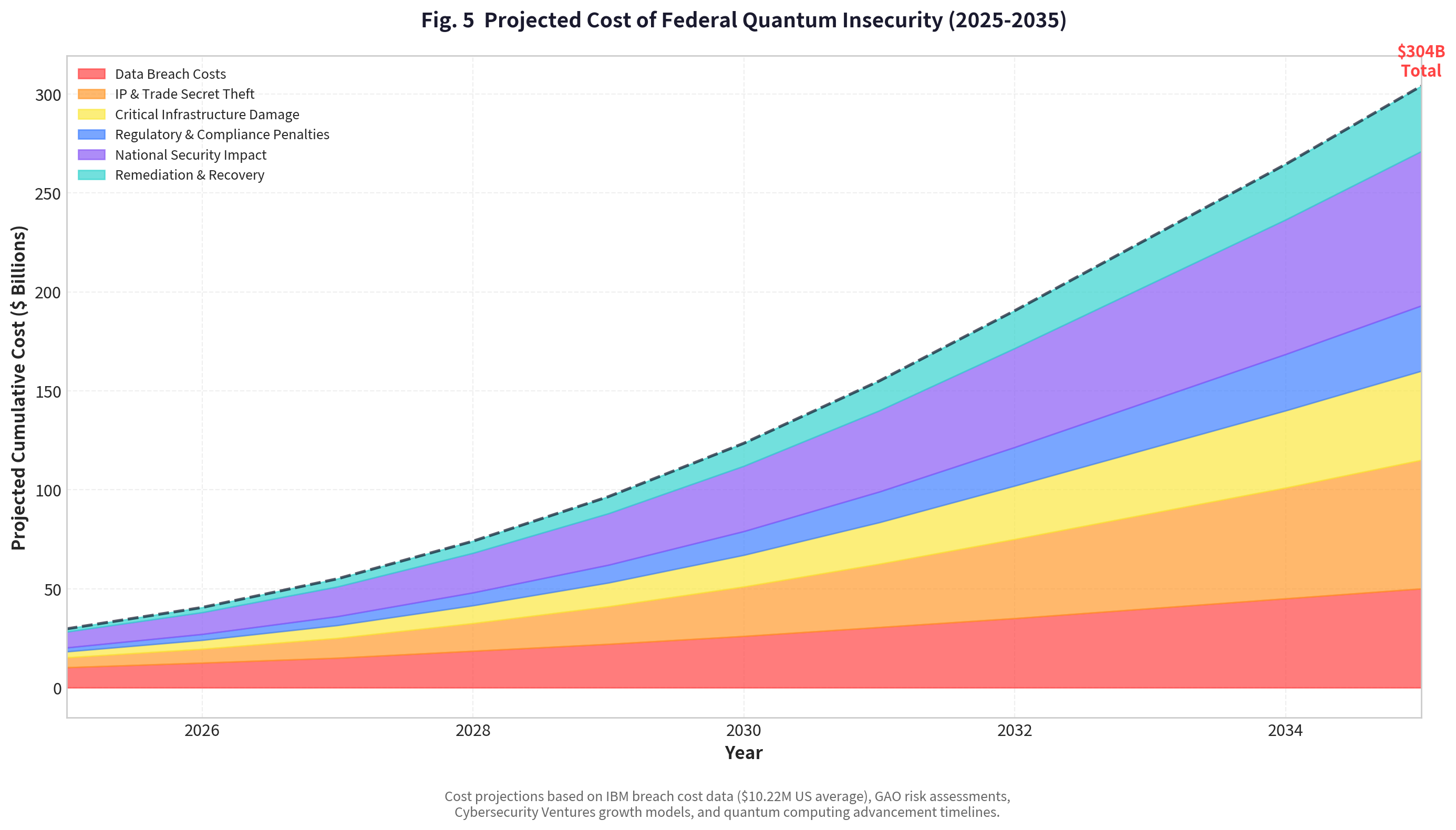
Stacked area chart projecting the cumulative financial impact of failing to achieve quantum safety across US federal agencies, broken down by cost category. Based on IBM breach cost data ($10.22M US average), GAO risk assessments, and Cybersecurity Ventures growth models.
PQC Investment vs. Potential Loss Avoidance by Department
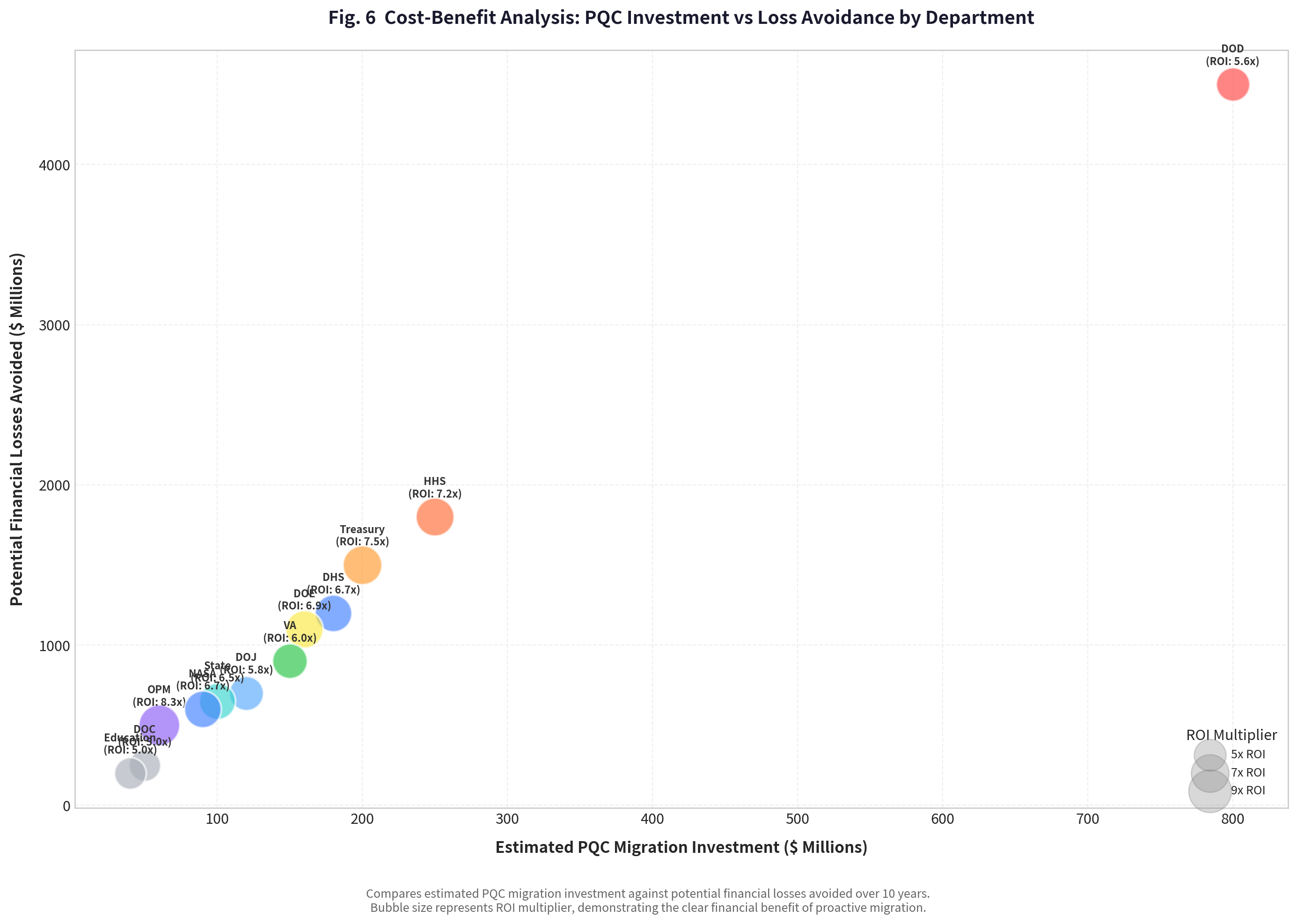
Compares estimated PQC migration investment against potential financial losses avoided over 10 years per federal department. Bubble size represents ROI multiplier, demonstrating the clear financial benefit of proactive migration aligned with CNSA 2.0 timelines.

moods.build × Never Local PQC Migration Roadmap
A four-phase migration roadmap aligned with NIST standards, NSA CNSA 2.0 requirements, and OMB M-23-02 directives — designed to ensure a smooth, secure, and cost-effective transition to Post-Quantum Cryptography across all federal agencies.
Discovery & Assessment
2025 – 2027
- Complete cryptographic asset inventory across all agencies
- Identify PKC/TLS/IPSec dependencies per department
- Assess HNDL risk exposure & data classification
- Build migration plan & budget framework (OMB M-23-02)
Priority Migration
2027 – 2030
- Deploy NIST PQC standards (FIPS 203/204/205)
- Migrate critical systems (DOD, NSA, Treasury priority)
- Implement hybrid cryptography (classical + PQC)
- VPN/TLS protocol migration to ML-KEM & ML-DSA
Full Deployment
2030 – 2033
- Complete migration of all federal agencies
- Decommission legacy crypto infrastructure
- IoT & ICS device firmware updates to PQC
- FedRAMP alignment & compliance verification
Continuous Assurance
2033 – 2035+
- Continuous cryptographic agility framework
- Real-time quantum threat monitoring & intelligence
- Automated PQC certificate rotation & management
- Ongoing governance & reporting to CISA/OMB
PQC Migration Strategic Roadmap (2025–2035+)
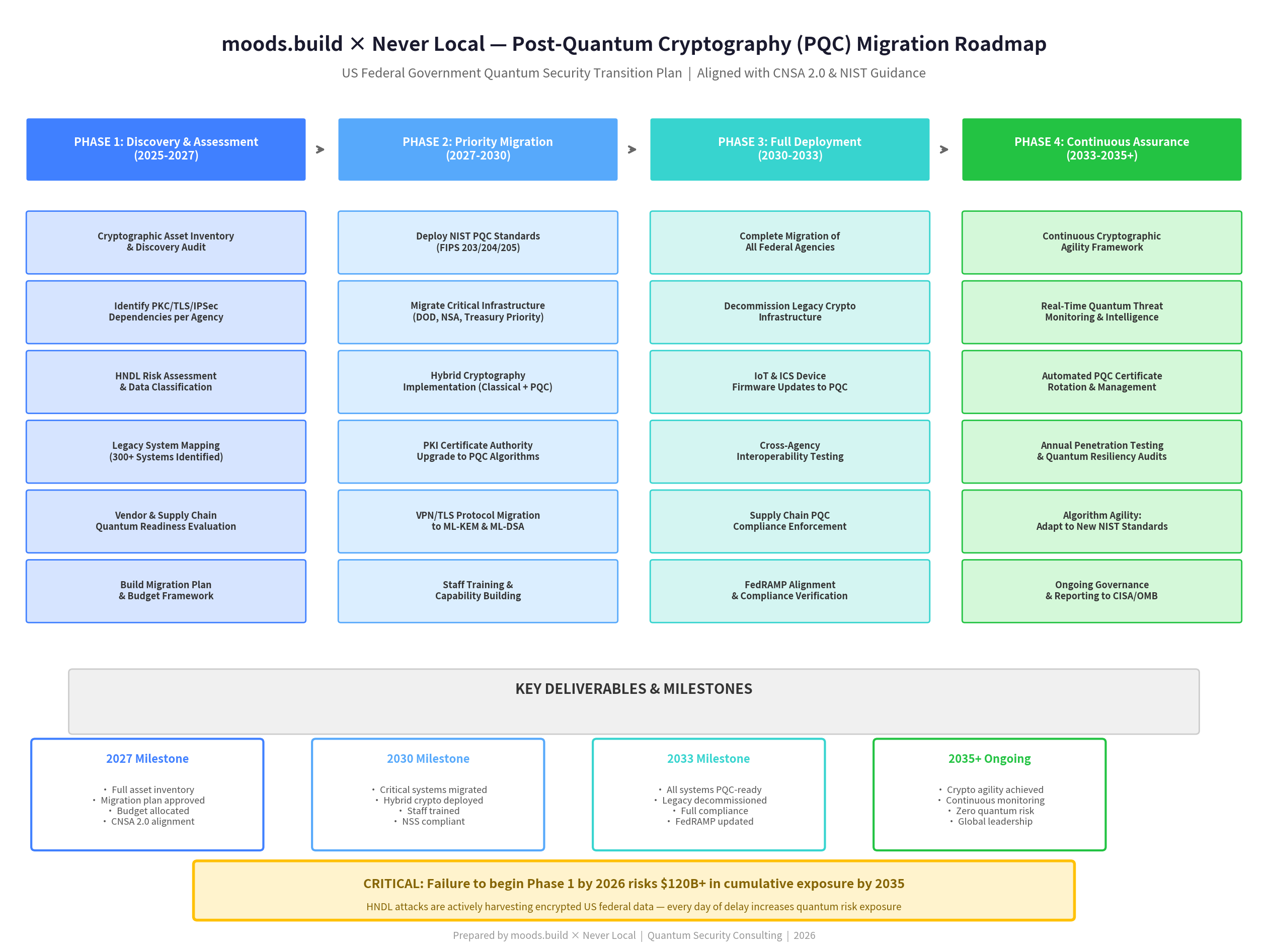
The proposed strategic roadmap for the US federal government's transition to Post-Quantum Cryptography, aligned with CNSA 2.0 and NIST guidance. Outlines key phases, activities, and milestones from 2025 to 2035 and beyond.
